Wie ein frei erhältliches Tool am Handy Tür und Tor öffnet
In den letzten Jahren hat sich die Nutzung von mobilen Endgeräten wie Smartphones und Tablets drastisch erhöht. Apps sind fixer Teil unseres Alltags geworden. Leider wird dabei häufig übersehen, dass diese Apps genauso IT-Security benötigen, wie herkömmliche Desktop-Anwendungen oder Webseiten.
Ein Fehler, der bei der Entwicklung dabei häufig auftritt, ist, dass man zwar Security-Features in die App implementiert, diese aber anschließend am Server nicht mehr geprüft werden. Eine App läuft ja immer auf dem Endgerät eines Benutzers und Hacker sind in der Lage diese App direkt anzugreifen. Dabei ergeben sich viele Angriffsoberflächen. So könnte die Kommunikation der App mit dem Server unterbrochen werden. Es können aber auch interne Daten der App am Endgerät nach Informationen durchsucht und schädliche Modifikationen vorgenommen werden. Auch exportierte Interfaces können geöffnet werden, wenn diese nicht über ausreichende Schutzmaßnahmen verfügen.
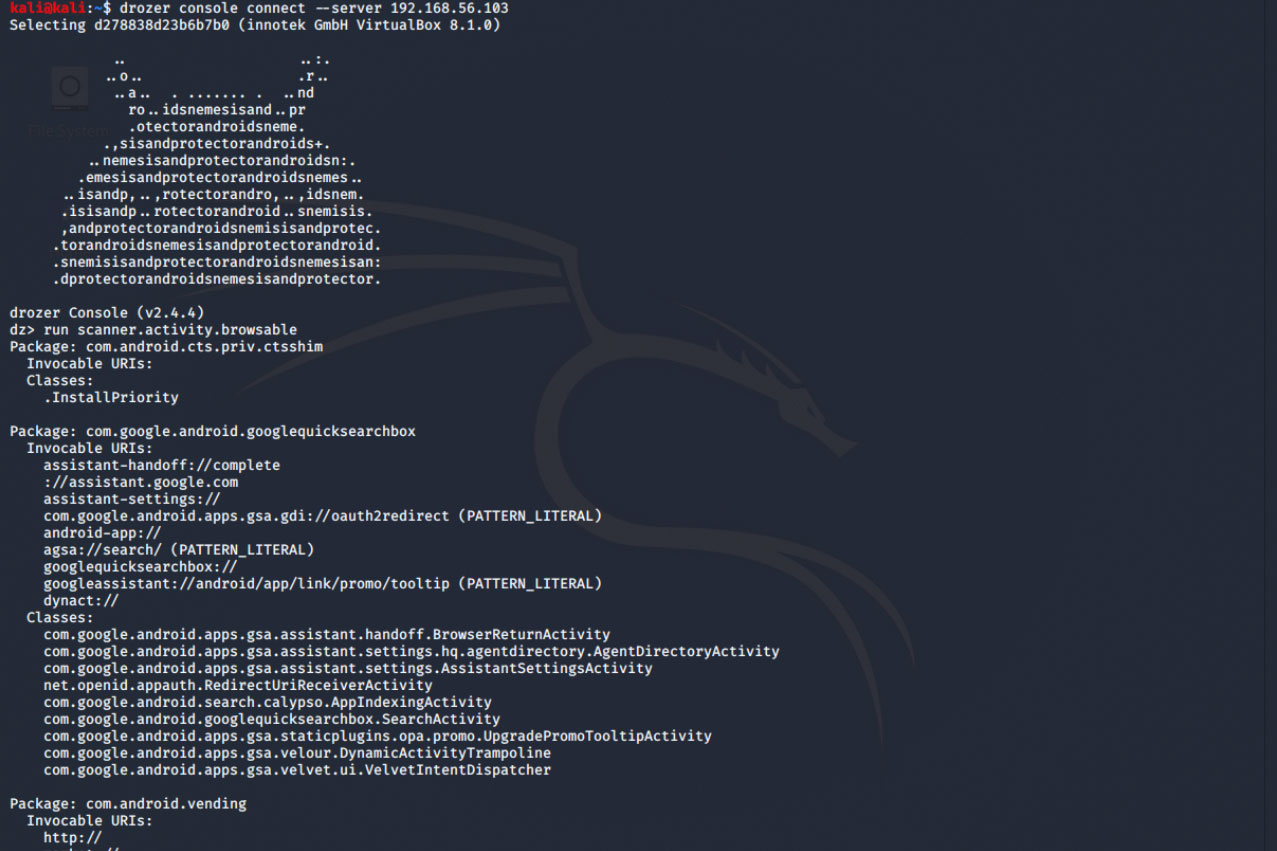
Ein Agent namens Drozer
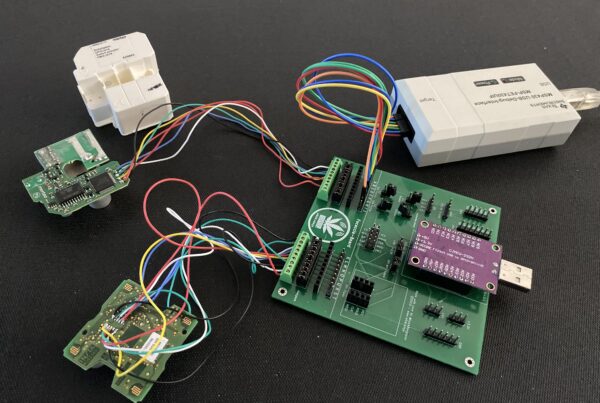
Ein bekanntes Tool hier ist Drozer. Ist der Drozer-Agent auf einem Smartphone installiert, so kann sich ein Angreifer mit diesem verbinden und Informationen über das Gerät absaugen. Drozer ist dabei in der Lage sich als eine native Android-Applikation auszugeben, mit der Dalvik Virtual Machine zu kommunizieren oder Informationen über das Betriebssystem zu sammeln. Zusätzlich erlaubt es Informationen über installierte Apps abzufragen, zum Beispiel aus der manifest.xml Datei. Das Tool kann dabei nicht nur Daten sammeln, sondern auch selbst Activities starten – dabei sind vor allem exportierte Activities, Broadcast Receivers, Content Providers und Services interessant. Wurden bei den genannten Schnittstellen keine ausreichenden Zugriffsrechte gesetzt, so kann Drozer diese nutzen, um interne Applikationsdaten auszulesen.
„Otto Normalverbraucher“ wird natürlich nicht freiwillig Drozer auf seinem Smartphone installieren, allerdings ist das meist auch nicht notwendig. Drozer kann als Teil einer legitimen App ausgeliefert werden, um sich unbemerkt auf dem Endgerät einzunisten, dazu kommt, dass es für seine Funktionalitäten nicht einmal Root-Rechte benötigt.
Limes empfiehlt:
Falls Sie selbst Apps entwickeln und sich nicht sicher sind, wie viele Informationen ein Drozer-Agent von Ihrer Applikation stehlen kann, bietet Limes Security Penetration an. Unsere Experten testen nicht nur die Angriffsoberfläche auf dem Smartphone, sondern auch andere kritische Komponenten Ihrer App.