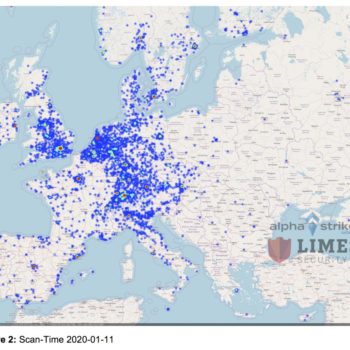
Seit dem 11.01.2020 führen die Alpha Strike Labs der Limes Security GmbH Scans nach verwundbaren Citrix-Systemen mit der Schwachstelle CVE-2019-19781 durch, welche gemäß aktuellen Medienberichten und Twitter-Kommentaren bereits aktiv ausgenutzt wird. Für die Scan-Erfassung wurde das auf dem CCCamp 2019 vorgestellte DCS-Scan-Netzwerk mit über 1.000 verschiedenen Suchknoten verwendet. [1]
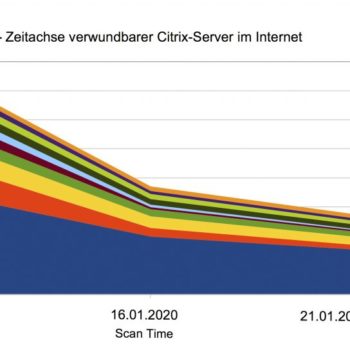
Eine zeitliche Analyse zeigt, dass Deutschland, Schweiz und die Niederlande am 21.01.2020 ca. 85 bis 90 Prozent der ursprünglich am 11.01.2020 verwundbaren Citrix-Server gepatcht haben. Andere Länder wie China, Frankreich und die USA erreichen hingegen nur eine Patch-Rate von 24 bis 56 Prozent. Zum 11. Jänner gab es weltweit 49.492 verwundbare Citrix-Server und am 21. Jänner waren immer noch 18.620 Systeme verwundbar.
In Deutschland waren ca. 24 Stunden nach der Bereitstellung des Citrix-Patches „nur“ noch ca. 800 und in Österreich 137 frei aus dem Internet zugängliche Citrix-Server von der Schwachstelle betroffen.
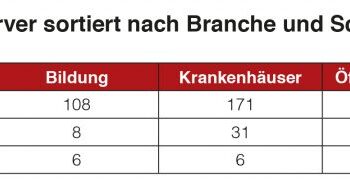
Waren zum ersten Scan-Zeitpunkt durch Alpha Strike Labs in der DACH-Region am 11.01.2020 noch 171 Kliniken und Krankenhäuser betroffen, so waren es ca. fünf Tage später nur noch 31 Citrix-Instanzen und weitere fünf Tage später nur noch sechs verwundbare Systeme. Allerdings waren auch über 140 Energieversorger, wie z. B. Stadtwerke zum ersten Scan-Zeitpunkt betroffen. Am Stichtag 21.01.2020 waren es noch immer 21 Versorger, die über einen verwundbaren Citrix-Service verfügten.
Ein großes Problem stellt auch der öffentliche Bereich, zu dem vor allem Landes- und Bundesbehörden zählen, dar. Hier waren am 11. Jänner noch 212 Server betroffen. Zehn Tage später (21.01.) waren es nur noch 21. Berücksichtigt man bei dieser Betrachtung, dass der erste Scan ca. drei Wochen nach dem Bekanntwerden der Schwachstelle Mitte-Dezember durchgeführt wurde, zeigt dies, dass auch die öffentliche Verwaltung einen gewissen Nachholbedarf im Bereich des Patch- bzw. Security-Managements hat.
Auf Spurensuche
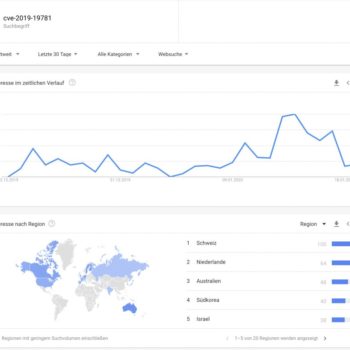
Die Analysen zeigen große Unterschiede zwischen den Ländern in Hinblick auf die Patch-Zeit. Eine Ursachenforschung fällt hier sehr schwer. Betrachtet man jedoch die Länder mit Google-Suchanfragen zu der Citrix-Schwachstelle mit der CVE-Nummer „cve-2019-19781“, erkennt man sofort, dass die Länder Schweiz und Niederlande mit dem höchsten Patch-Level von 90 Prozent auch die Länder mit den meisten Suchanfragen nach dieser Schwachstelle sind. [2]
Weiters lässt sich schnell erkennen, dass ab dem 13. Jänner 2020 das Interesse der Google-Nutzer an der Schwachstelle stark gestiegen ist. Zeitgleich zeigt sich anhand der Scan-Daten, dass nach dem 13. Jänner die Absicherung der Systeme ebenfalls stark zugenommen hat. Dies steht sicherlich auch im Zusammenhang mit der vermehrten medialen Berichterstattung.
Fazit
Einerseits ist es gut, dass viele Systeme nun nicht mehr über diese Schwachstelle verfügen, andererseits ist es erschreckend, wie lange es dauert, bis das Einspielen des Patches bzw. des Hotfixes bei den Betreibern dieser Systeme weltweit umgesetzt ist.
Mehr Informationen zu diesem Fall und wie man schnell darauf reagiert, bietet das Team der Limes Security – kontaktieren Sie uns!